In an age where misconfigurations outpace traditional breaches, organizations must embrace proactive measures. Cloud Posture Management empowers businesses to fortify their defenses, ensuring security and peace of mind in a rapidly evolving digital landscape.
Misconfigurations Are the New Data Breach: How Cloud Posture Management Helps
In today’s digital landscape, where the lifeblood of businesses flows through the cloud, a new specter looms over data security—misconfigurations. As organizations rush to adopt cloud technologies, the complexity of these environments often leads to unintentional vulnerabilities that can expose sensitive information and erode customer trust. Just as we’ve learned to guard against traditional data breaches, we must now confront this insidious risk that lurks behind the screens of our cloud infrastructures. But fear not; there is hope. Cloud Posture Management emerges as a beacon of resilience, offering a comprehensive approach to safeguard our digital assets and ensure compliance in an ever-evolving threat landscape. In this article, we will explore how embracing proactive posture management not only mitigates the risks of misconfigurations but empowers organizations to operate with confidence, transforming potential pitfalls into opportunities for growth and innovation. Join us on a journey to fortify our cloud environments and secure a brighter, more secure future.
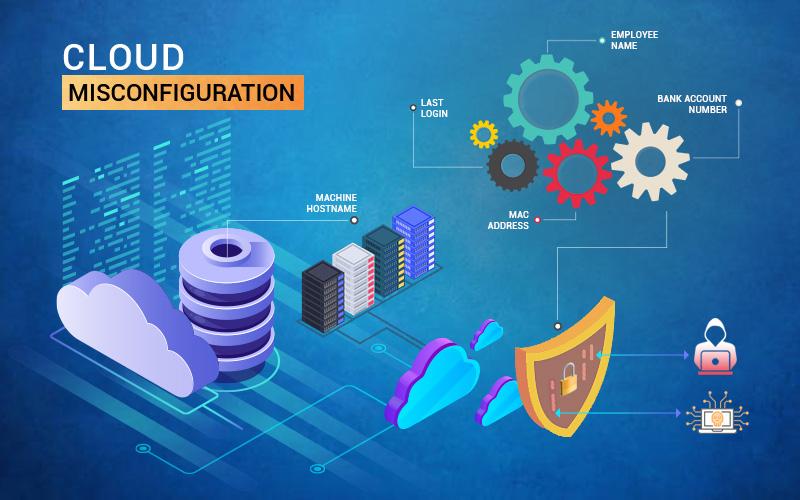
Understanding the Silent Threat of Misconfigurations in the Cloud
In the rapidly evolving landscape of cloud computing, organizations often feel the pressure to innovate and deploy services at an unprecedented pace. However, this urgency can inadvertently lead to misconfigurations—a silent yet potent threat lurking in the shadows. Misconfigurations can open the door to security vulnerabilities, exposing sensitive data and disrupting operations. As enterprises increasingly migrate to the cloud, the need for robust cloud posture management becomes essential.
Misconfigurations can manifest in various forms, including:
- Exposed Storage Buckets: Publicly accessible storage that can lead to data leaks.
- Weak Security Groups: Inadequate firewall rules allowing unnecessary access.
- Unrestricted API Access: APIs that can be exploited if not properly secured.
- Default Credentials: Failure to change default passwords that cybercriminals readily exploit.
Consider the implications of a single misconfiguration. A well-known cloud service provider experienced a significant data breach due to an unsecured storage bucket, resulting in the exposure of millions of sensitive records. Such incidents not only damage reputations but also incur hefty financial penalties and regulatory scrutiny. Cloud posture management tools can proactively identify and remediate these vulnerabilities before they escalate into full-blown crises.
Leveraging advanced cloud posture management solutions offers organizations a robust defense against misconfigurations. These tools provide:
- Continuous Monitoring: Real-time insights into cloud configurations and security postures.
- Automated Compliance Checks: Ensuring adherence to industry regulations and best practices.
- AI-Driven Analytics: Identifying potential misconfigurations through intelligent analysis.
- Remediation Guidance: Offering actionable steps to rectify identified issues.
Implementing a proactive strategy for cloud posture management is not merely a technical necessity; it is a strategic imperative. By fostering a culture of security awareness and investing in the right tools, organizations can significantly reduce the risk associated with misconfigurations. This approach not only fortifies defenses but also empowers teams to focus on innovation rather than firefighting security issues.
Ultimately, the journey towards a secure cloud environment demands vigilance, education, and the right technology. As organizations embrace the limitless possibilities of the cloud, addressing misconfigurations head-on will position them as leaders in security and innovation.
The Evolution of Data Breaches: Why Misconfigurations Are the New Norm
As organizations increasingly migrate to the cloud, the landscape of data breaches has dramatically shifted. While traditional data breaches often stemmed from malicious hacking or insider threats, the current trend reveals a startling truth: misconfigurations are becoming the primary culprits behind security compromises. The ease of deploying cloud infrastructures has unfortunately resulted in a rise in configuration errors that can expose sensitive data to unauthorized access.
Cloud services offer incredible flexibility and scalability, but with this power comes the responsibility of proper configuration. Common misconfigurations include:
- Default settings not being changed.
- Excessive permissions granted to users.
- Public access to sensitive resources.
- Failure to implement proper identity and access controls.
Each of these missteps can lead to significant vulnerabilities, providing cybercriminals with easy entry points. A single misconfiguration can turn a well-intentioned deployment into a gaping hole that can expose critical data, leading to reputational damage and financial loss.
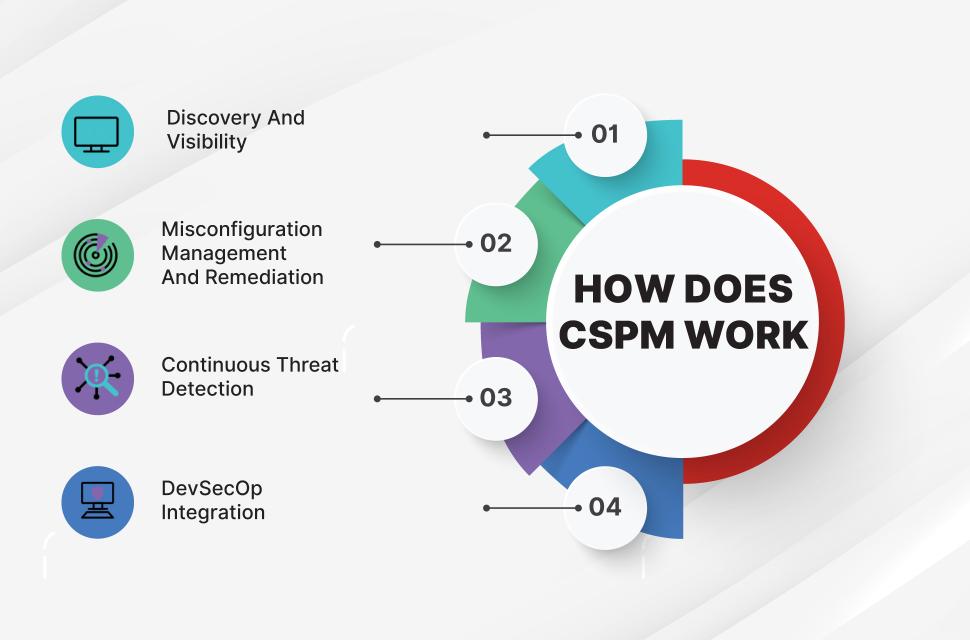
To combat the increasing threat of misconfigurations, organizations are turning to Cloud Posture Management (CPM) solutions. These tools play a vital role in identifying and rectifying configuration issues before they can be exploited. Here’s how CPM solutions contribute to a healthier cloud environment:
- Automated Checks: Continuous monitoring of cloud environments to detect misconfigurations in real-time.
- Compliance Enforcement: Ensuring that cloud setups adhere to industry standards and regulations.
- Risk Assessment: Evaluating the potential impact of configuration errors and prioritizing remediation efforts.
- User Education: Providing insights and training to prevent future misconfigurations.
Consider a simple comparison table that illustrates the effectiveness of conventional security measures versus CPM:
| Security Measure | Effectiveness Against Misconfigurations | Real-time Monitoring |
|---|---|---|
| Traditional Security Audits | Limited | No |
| Cloud Posture Management | High | Yes |
This table exemplifies why reliance on outdated security practices is no longer tenable in a cloud-centric world. As cyber threats evolve, so must our defenses. By adopting a proactive approach through CPM, organizations can not only mitigate the risks associated with misconfigurations but also foster a culture of security awareness and responsibility among their teams.
In this era of digital transformation, it’s time for organizations to shift their focus. Embracing Cloud Posture Management is not merely a strategic advantage; it’s an imperative for ensuring that your data remains secure and your business resilient. By prioritizing prevention over reaction, businesses can thrive in the cloud without falling victim to the pitfalls of misconfiguration.
The Hidden Costs of Cloud Misconfigurations: Protecting Your Bottom Line
In a world where cloud computing reigns supreme, the allure of scalable resources and on-demand flexibility can often lead organizations to overlook critical details. One such detail is the configuration of cloud environments, which can become the Achilles’ heel for many businesses. Misconfigurations, rather than external attacks, are increasingly recognized as a primary risk factor, capable of inflicting significant financial damage and tarnishing reputations.
Consider the following hidden costs associated with cloud misconfigurations:
- Data Breaches: Inadequately secured configurations can expose sensitive data, resulting in compliance fines and loss of customer trust.
- Downtime: Configuration errors can lead to system outages, causing operational interruptions that directly impact revenue generation.
- Increased Management Costs: The time and resources spent on remediation can divert attention from strategic initiatives, inflating operational expenses.
- Legal Liabilities: Misconfigurations can lead to violations of regulations such as GDPR or HIPAA, exposing organizations to potential lawsuits and penalties.
To illustrate the financial impact, a recent study highlighted that nearly 90% of organizations experience at least one misconfiguration incident annually, with costs averaging upwards of $5 million per occurrence. The table below summarizes the potential financial repercussions of various misconfigurations:
| Type of Misconfiguration | Average Cost ($) |
|---|---|
| Data Exposure | 1,500,000 |
| Service Downtime | 2,000,000 |
| Compliance Fines | 1,000,000 |
| Security Incident Response | 500,000 |
Implementing a robust cloud posture management strategy is no longer optional; it is essential. These solutions are designed to automatically detect misconfigurations, provide actionable insights, and implement remediation to prevent disasters before they occur. By proactively managing cloud configurations, organizations can:
- Enhance Security: Regular audits and automated compliance checks fortify defenses against breaches.
- Reduce Costs: Lower the risk of financial fallout from configuration errors that can spiral out of control.
- Boost Efficiency: Streamline operations by eliminating the need for extensive recovery efforts.
When businesses recognize the hidden costs of misconfigurations, they can take decisive action to protect their bottom line. Investing in cloud posture management not only mitigates risks but also positions organizations for sustained growth in an increasingly complex digital landscape.
Building a Strong Foundation: The Importance of Cloud Posture Management
In today’s rapidly evolving digital landscape, the complexity of cloud environments is unprecedented. Organizations often find themselves juggling multiple services, configurations, and compliance requirements, leading to an increased risk of misconfigurations—a threat that has become synonymous with data breaches. Emphasizing the crucial role of effective cloud posture management can transform how organizations safeguard their data and maintain their integrity.
Cloud posture management is not merely a protective measure; it is a proactive strategy that empowers organizations to:
- Identify Vulnerabilities: By continuously monitoring cloud configurations, businesses can detect weaknesses before they are exploited.
- Enhance Compliance: Automated checks ensure that configurations adhere to regulatory standards, reducing the risk of penalties.
- Optimize Resource Usage: Effective posture management enhances efficiency, potentially lowering operational costs while boosting security.
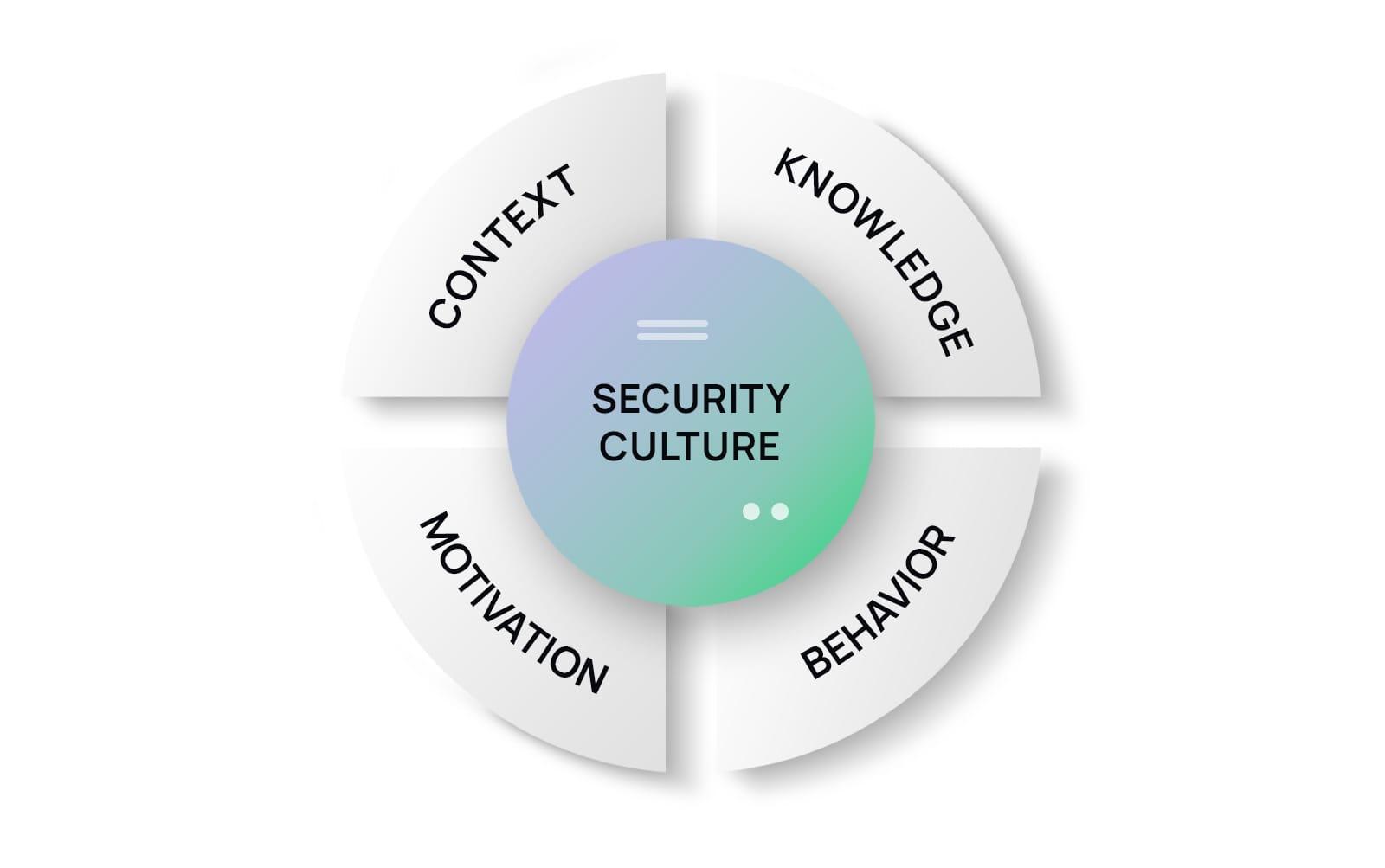
One of the most significant aspects of cloud posture management is its ability to facilitate a culture of security within the organization. Teams become more aware of the intricacies of cloud configurations and their implications, leading to better decision-making. This cultural shift not only mitigates risks but also fosters a sense of responsibility among employees, making security a shared value.
To illustrate the profound impact of cloud posture management, consider the following:
| Risk Type | Impact of Misconfiguration | Posture Management Solutions |
|---|---|---|
| Data Breaches | Exposure of sensitive information | Automated configuration auditing |
| Compliance Failures | Substantial fines and reputational damage | Regulatory compliance dashboards |
| Service Disruptions | Downtime and loss of productivity | Real-time monitoring alerts |
Moreover, implementing robust cloud posture management tools enables organizations to respond swiftly to threats. With real-time insights and automated remediation, businesses can address potential issues before they escalate. This not only protects assets but also builds trust with customers and partners.
Ultimately, the journey towards a secure cloud environment starts with a commitment to understanding and managing configurations diligently. Organizations that prioritize cloud posture management position themselves not just as compliant entities, but as leaders in security and innovation, ready to navigate the complexities of the cloud with confidence and resilience.
Key Principles of Effective Cloud Posture Management for Security
In the rapidly evolving world of cloud computing, ensuring robust security is paramount. Effective Cloud Posture Management focuses on the configuration and governance of cloud environments, aiming to minimize vulnerabilities that can lead to misconfigurations. By adhering to fundamental principles, organizations can protect their assets and data from the fallout of security breaches.
- Continuous Monitoring: Regularly assess cloud configurations to identify deviations from best practices. Automated tools can alert teams to potential risks in real-time, ensuring swift corrective action.
- Least Privilege Access: Implement a strict access control policy that gives users only the permissions necessary for their jobs. This minimizes the risk of unauthorized access and accidental misconfigurations.
- Configuration Standards: Establish clear and concise configuration benchmarks based on industry standards. Regular audits against these benchmarks help maintain a secure posture.
- Automated Remediation: Utilize tools that not only detect misconfigurations but also automatically rectify them. This reduces human error and enhances security efficiency.
- Education and Training: Regularly train staff on cloud security best practices. An informed team is less likely to create vulnerabilities through oversight.
Integrating these principles into an organization’s cloud strategy isn’t just about compliance; it’s about building a culture of security that permeates every level. When teams understand the risks associated with misconfigurations, they become proactive in safeguarding their environments. By fostering a mindset where security is everyone’s responsibility, organizations can significantly reduce their attack surface.
Furthermore, collaboration between security, operations, and development teams is essential. DevSecOps, as an approach, emphasizes integrating security into the development process, ensuring that security considerations are built in from the ground up. This collaborative effort enhances security posture and encourages innovation without compromising safety.
| Security Principle | Benefit |
|---|---|
| Continuous Monitoring | Real-time threat detection and rapid response |
| Least Privilege Access | Minimized risk of data exposure |
| Configuration Standards | Consistency in secure settings across environments |
| Automated Remediation | Reduced manual errors and faster recovery |
| Education and Training | Empowered teams capable of making informed decisions |
Ultimately, the goal of effective cloud posture management transcends mere compliance; it aims to create a resilient framework that evolves alongside emerging threats. By embedding these principles into the organizational fabric, businesses can confidently navigate the complexities of cloud security, transforming potential vulnerabilities into strengths.

Real-World Case Studies: Lessons Learned from Misconfigured Clouds
Recent incidents have underscored the profound implications of cloud misconfigurations. One notable example is the data exposure incident involving a prominent financial services firm, which mistakenly left their cloud storage buckets publicly accessible. This oversight resulted in the leakage of sensitive customer data, including social security numbers and account details. The repercussions were not just financial; the firm’s reputation suffered significantly, leading to a loss of customer trust that took years to rebuild.
Another striking case involved a major healthcare provider that inadvertently configured its cloud database without proper security protocols. Hackers exploited this misconfiguration, accessing personal health information of millions of patients. The aftermath was catastrophic, involving hefty fines and mandatory audits, alongside the erosion of patient confidentiality that is the bedrock of healthcare trust.
Key Lessons Learned:
- Prioritize Security Configurations: Organizations must ensure that security policies are not just an afterthought but are integrated into the cloud deployment process from the outset.
- Regular Audits and Monitoring: Continuous monitoring of cloud configurations is crucial. Automated tools can help in identifying vulnerabilities and misconfigurations before they lead to significant breaches.
- Employee Training and Awareness: Human error is often a contributing factor to misconfigurations. Providing regular training can empower teams to recognize potential security risks.
In a particularly alarming case, a cloud service provider left an API endpoint insecurely configured, allowing unauthorized access to a comprehensive dataset of user information. Fortunately, the vulnerability was discovered by a cybersecurity researcher before it could be exploited maliciously. This incident highlighted the importance of proactively testing and securing APIs, which are often the gateways to sensitive data.
To illustrate the impact of misconfigurations, consider the following table summarizing key incidents and their consequences:
| Incident | Type of Data Exposed | Consequence |
|---|---|---|
| Financial Services Firm | Customer Data | Loss of Trust & Financial Penalties |
| Healthcare Provider | Personal Health Information | Hefty Fines & Legal Repercussions |
| Cloud Service Provider | User Information | Potential Exploitation & Reputation Damage |
these real-world case studies serve as a clarion call for organizations operating in the cloud. The lessons learned are clear: proactive management of cloud configurations is not merely a preventive measure; it is essential for safeguarding sensitive information and maintaining trust in today’s digital landscape.

Empowering Your Teams: Best Practices for Cloud Configuration Awareness
In the ever-evolving landscape of cloud technologies, ensuring that your teams are equipped with the knowledge and skills to manage configurations effectively is crucial. Misconfigurations can lead to dire consequences, often paralleling the impact of data breaches. To mitigate these risks, organizations must invest in empowering their teams through comprehensive training and awareness initiatives.
Fostering a Culture of Awareness: Building a culture that prioritizes cloud configuration awareness can significantly enhance your organization’s security posture. Encouraging open communication about configuration changes, potential risks, and best practices ensures that all team members are on the same page. Regular team meetings and workshops can serve as platforms for discussing real-world scenarios and learning from past missteps.
- Conduct Regular Training: Implement ongoing training programs to keep your teams updated on the latest cloud security practices and configuration management techniques.
- Create Clear Documentation: Develop easily accessible documentation that outlines approved configuration settings and common pitfalls.
- Encourage Peer Reviews: Foster a collaborative environment where team members can review each other’s configurations before deployment.
Utilizing Cloud Posture Management Tools: Integrating cloud posture management tools can empower teams to maintain optimal configuration settings. These tools provide real-time visibility into your cloud environment, identifying misconfigurations and compliance issues before they escalate into security threats. By leveraging automated checks and balances, organizations can ensure that their configurations are always aligned with best practices.
Promoting Accountability: It’s essential to instill a sense of ownership among team members regarding their roles in cloud configuration management. Establishing accountability measures, such as assigning specific configuration responsibilities to individuals or teams, can enhance the overall effectiveness of your cloud security strategy. Recognizing and rewarding team members who proactively identify and rectify misconfigurations fosters a positive feedback loop that reinforces best practices.
Establishing Metrics for Success: To gauge the effectiveness of your cloud configuration awareness initiatives, establish clear metrics that reflect improvement over time. Metrics could include the number of misconfigurations detected and resolved, the speed of patch implementation, or the frequency of security incidents related to configuration errors. Regularly reviewing these metrics with your teams can highlight successes and identify areas for further improvement.
| Best Practice | Description |
|---|---|
| Regular Audits | Conduct audits to identify and rectify misconfigurations proactively. |
| Use of Automation | Implement automated tools to continuously monitor and correct configuration settings. |
| Incident Response Plans | Develop and rehearse plans to respond to configuration-related incidents efficiently. |
By embedding these best practices into your organizational fabric, you arm your teams with the necessary tools to navigate the complexities of cloud configurations confidently. Together, you can transform potential vulnerabilities into strengths, ensuring that your cloud environment remains secure and resilient against evolving threats.

Proactive Monitoring: The Role of Automation in Cloud Security
In today’s cloud-centric world, where data is the lifeblood of organizations, maintaining security is more critical than ever. Proactive monitoring provides a robust defense against the ever-evolving landscape of threats. By leveraging automation, companies can transform their approach to cloud security, ensuring that potential vulnerabilities are identified and mitigated before they escalate into full-blown incidents.
Automation enables continuous oversight of cloud resources, offering several key advantages:
- Real-time Alerts: Automated systems can instantly detect misconfigurations and send alerts, allowing security teams to respond promptly.
- Consistent Compliance Checks: Automation ensures that security policies are uniformly applied across all cloud environments, reducing the likelihood of human error.
- Enhanced Visibility: With automated monitoring tools, organizations can gain insights into their cloud configurations, identifying areas of risk that may have gone unnoticed.
One of the most significant benefits of automation in cloud security is its ability to reduce response times. When a potential misconfiguration is detected, automated systems can not only notify the relevant teams but can also initiate predefined remediation actions. This swift action minimizes the window of exposure and helps maintain the integrity of sensitive data.
Furthermore, automation plays a crucial role in scalability. As organizations grow and their cloud architectures become increasingly complex, manually monitoring configurations becomes impractical. Automated tools can seamlessly scale to accommodate new services, ensuring that cloud security remains robust regardless of size or complexity.
To illustrate the importance of proactive monitoring, consider this simple table showcasing common cloud misconfigurations and their potential impacts:
| Misconfiguration | Potential Impact |
|---|---|
| Publicly Accessible Storage Buckets | Data Exposure & Breaches |
| Weak IAM Policies | Unauthorized Access |
| Unrestricted API Access | Data Manipulation |
| Improperly Configured Security Groups | Network Attacks |
By investing in cloud posture management solutions that prioritize proactive monitoring, organizations can significantly enhance their security posture. The synergy between automation and cloud security not only leads to better compliance and risk management but also fosters a culture of continuous improvement. This approach ensures that security is not merely reactive but becomes an integral part of the organization’s operational framework.

Navigating Compliance and Governance in a Misconfiguration-Prone World
As organizations continue to embrace cloud technologies, the landscape of compliance and governance is evolving at a breakneck pace. Misconfigurations in cloud environments have emerged as significant vulnerabilities, often leading to data breaches and compliance failures. Addressing these issues demands a proactive approach that integrates robust cloud posture management strategies to safeguard sensitive information while maintaining regulatory compliance.
To effectively navigate the complexities of compliance and governance, organizations must prioritize the following elements:
- Continuous Monitoring: Implementing tools that provide continuous oversight of cloud configurations can identify vulnerabilities before they are exploited.
- Automated Compliance Checks: Automating compliance assessments against industry standards ensures that any deviations from required practices are promptly addressed.
- Real-Time Alerts: Establishing alert mechanisms for misconfigurations allows teams to respond swiftly to potential threats, minimizing risk exposure.
- Regular Training and Awareness: Equipping employees with knowledge about common misconfigurations fosters a culture of security mindfulness throughout the organization.
Moreover, organizations should consider leveraging cloud posture management solutions that offer a comprehensive view of their cloud environments. These solutions provide a unified platform for:
| Feature | Benefit |
|---|---|
| Configuration Assessment | Identifies misconfigurations and recommends corrective actions. |
| Risk Management | Evaluates the risk associated with specific configurations and prioritizes remediation efforts. |
| Policy Enforcement | Ensures that all cloud resources adhere to organizational governance policies. |
| Reporting and Analytics | Provides insights into compliance status and highlights areas needing improvement. |
In an era where data breaches have devastating consequences, organizations must recognize that the cost of misconfigurations is not just financial; it can tarnish reputations and erode customer trust. By integrating cloud posture management into their governance frameworks, companies can transform potential vulnerabilities into strengths, ensuring compliance while fostering innovation.
Ultimately, embracing a culture of security through continuous improvement, education, and the right tools will prepare organizations to thrive in a misconfiguration-prone world. This proactive mindset is essential not just for protecting assets but also for enabling business growth in a cloud-centric future.

Integrating Security into DevOps: A Collaborative Approach to Cloud Safety
In today’s cloud-centric landscape, the intersection of DevOps and security has become a critical focus for organizations aiming to safeguard their digital assets. Misconfigurations in cloud environments are not just a minor oversight; they can lead to significant vulnerabilities, exposing sensitive data and critical infrastructure to malicious actors. By adopting a collaborative approach that integrates security into every phase of the DevOps lifecycle, businesses can proactively mitigate risks and fortify their cloud posture.
Collaboration Across Teams
Bringing together development, operations, and security teams is essential for creating a culture of shared responsibility. When these teams work in silos, it often leads to gaps that can be exploited. By fostering open communication and collaboration, organizations can ensure that security considerations are embedded in every stage of development. This collaborative spirit promotes:
- Knowledge Sharing: Teams can exchange insights about potential vulnerabilities and mitigation strategies.
- Continuous Improvement: Feedback loops allow for rapid identification and resolution of security issues.
- Increased Agility: Security measures can be adapted quickly to meet evolving threats without hindering continuous deployment.
Incorporating Security Measures Early
Integrating security into the early stages of the DevOps process—often referred to as “shifting security left”—is crucial. This includes implementing automated security testing and compliance checks as part of the build pipeline. By identifying vulnerabilities before code reaches production, organizations can save time and resources while enhancing overall security posture. Here are some key practices:
- Static Application Security Testing (SAST): Analyze source code for vulnerabilities before deployment.
- Dynamic Application Security Testing (DAST): Test running applications to identify security weaknesses in real-time.
- Infrastructure as Code (IaC) Scanning: Ensure cloud configurations align with security best practices.
Leveraging Cloud Posture Management
Cloud Posture Management (CPM) plays a vital role in maintaining a secure cloud environment. By continuously monitoring configurations and compliance, CPM tools can help organizations quickly identify and remediate misconfigurations that may lead to data breaches. These tools provide:
- Real-time Alerts: Immediate notifications of configuration changes that introduce risk.
- Compliance Reporting: Automated assessments against industry standards and frameworks.
- Risk Visualization: Dashboards that present security posture in an easy-to-understand format.
The Road Ahead
As cloud adoption continues to rise, the emphasis on security will only become more paramount. Organizations that embrace a culture of collaboration and actively integrate security into their DevOps processes will not only reduce the risk of misconfigurations but also build a resilient framework for future growth. By leveraging tools like Cloud Posture Management, teams can take proactive steps to ensure the safety of their cloud environments while maintaining the velocity needed for innovation.
| Key Benefits | Impact on Security |
|---|---|
| Enhanced Collaboration | Reduces blind spots and improves threat response. |
| Proactive Security Testing | Identifies vulnerabilities before they can be exploited. |
| Continuous Monitoring | Ensures compliance and reduces the risk of misconfigurations. |

Choosing the Right Tools: Essential Features for Cloud Posture Management Solutions
In an era where cloud adoption is skyrocketing, ensuring that your cloud infrastructure remains secure is paramount. The right Cloud Posture Management (CPM) tool can be the difference between a robust security posture and a catastrophic data breach. When evaluating CPM solutions, consider the following essential features that can empower your organization to maintain compliance, visibility, and control over its cloud environments.
- Continuous Monitoring: The ability to continuously scan your cloud environment for misconfigurations and vulnerabilities is crucial. Look for tools that provide real-time alerts, enabling you to address issues before they lead to breaches.
- Automated Compliance Checks: Compliance can be daunting. A good CPM solution should offer automated compliance frameworks that ensure adherence to regulations such as GDPR, HIPAA, and PCI-DSS. This feature not only saves time but also reduces human error.
- Integration Capabilities: Your CPM tool should seamlessly integrate with existing security tools and workflows. This interoperability enhances the visibility of your security posture across various platforms, enabling you to respond to threats more effectively.
- User-Friendly Dashboards: A clear and intuitive interface is vital for effective decision-making. Look for CPM solutions that provide dashboards with actionable insights, making it easy to track compliance status and security issues.
- Risk Assessment Features: Understanding the risk associated with each cloud asset is essential. Advanced CPM tools offer risk assessment features that categorize and prioritize issues based on potential impact, helping you allocate resources efficiently.
Additionally, consider how a CPM solution handles remediation. The best tools not only identify misconfigurations but also provide guided remediation steps or automated fixes. This not only expedites the resolution process but also ensures that your cloud environment remains secure without significant manual intervention.
a strong community and support system can enhance the effectiveness of your CPM tool. Look for platforms that offer extensive documentation, forums, and direct support options. A vibrant community can provide invaluable insights and best practices that can help you leverage the tool to its fullest potential.
| Feature | Importance |
|---|---|
| Continuous Monitoring | Identifies threats in real-time. |
| Automated Compliance Checks | Reduces manual oversight and errors. |
| Integration Capabilities | Enhances visibility across tools. |
| User-Friendly Dashboards | Facilitates quick decision-making. |
| Risk Assessment Features | Prioritizes remediation efforts effectively. |
| Guided Remediation | Speeds up the fixing of issues. |
Creating a Culture of Security: Training and Awareness for Your Organization
In today’s digital landscape, protecting sensitive data is no longer solely an IT responsibility; it requires a collective effort across every level of an organization. As organizations increasingly migrate to cloud environments, the risk of misconfigurations also rises, making it imperative to cultivate a culture of security. This begins with comprehensive training and awareness programs designed to equip every employee with the knowledge they need to recognize and mitigate potential threats.
Investing in Training Programs is essential for fostering an environment where security is at the forefront. Regular workshops and seminars can help demystify complex security concepts. They should cover topics such as:
- Understanding the shared responsibility model in cloud security
- Identifying common misconfigurations and their impacts
- Best practices for managing sensitive data
- Incident response protocols and reporting procedures
To further enhance awareness, organizations can implement simulated phishing attacks and other hands-on exercises. These practical experiences not only reinforce learning but also improve the employees’ ability to respond to real-world threats. Creating a safe space for employees to practice their decision-making skills in security scenarios can significantly reduce the chances of human error leading to data breaches.
Additionally, establishing a security champions program can cultivate leaders within teams who advocate for best practices. These champions can bridge the gap between IT and other departments, ensuring consistent messaging and fostering a proactive security mindset throughout the organization. They can also serve as points of contact for colleagues seeking guidance on security matters, promoting collaboration and open communication.
To measure the effectiveness of these initiatives, organizations should conduct regular assessments and feedback surveys. This data can help identify knowledge gaps and areas for improvement, ensuring that training remains relevant and impactful. Below is a simple table that outlines potential metrics for evaluating training success:
| Metric | Description | Target Outcome |
|---|---|---|
| Employee Engagement | Participation rates in training sessions | 80%+ attendance |
| Knowledge Retention | Post-training assessment scores | 75%+ correct answers |
| Incident Reporting | Number of reported incidents post-training | Increase in reporting |
Ultimately, fostering a culture of security is about transforming mindsets where every employee feels accountable for protecting data. By investing in robust training and awareness programs, organizations not only reduce the likelihood of misconfigurations and data breaches but also empower their workforce to become active participants in safeguarding the organization’s digital assets. In this collaborative approach, security becomes a shared responsibility, seamlessly woven into the fabric of the organizational culture.

Future-Proofing Your Cloud Security Strategy: Embracing Change and Adaptability
As organizations increasingly migrate to the cloud, the landscape of security threats evolves alongside these advancements. Today, misconfigurations are not just a minor oversight; they are a primary vector for data breaches and can leave sensitive information vulnerable to attack. To combat this, implementing a robust Cloud Posture Management (CPM) strategy is essential for any forward-thinking business.
Cloud environments are dynamic, necessitating a security approach that is both flexible and proactive. By embracing continual change, organizations can adapt their security policies and tools to match the rapidly evolving threat landscape. This adaptability ensures that potential gaps caused by misconfigurations are swiftly identified and corrected, averting disastrous breaches before they occur.
Key components of an effective Cloud Posture Management strategy include:
- Continuous Monitoring: Implement 24/7 surveillance of cloud configurations to swiftly detect and rectify misconfigurations.
- Automated Compliance Checks: Regularly validate configurations against industry standards and best practices to maintain compliance.
- Incident Response Plans: Develop and rehearse action plans to respond rapidly to any identified vulnerabilities.
- Employee Training: Educate staff on common misconfigurations and how to avoid them, fostering a culture of security awareness.
Moreover, leveraging automation tools within your CPM strategy can significantly reduce the likelihood of human error, which is often a leading cause of misconfigurations. These tools can automatically adjust settings based on predefined security policies, ensuring that your cloud environment is consistently aligned with best practices.
| Type of Misconfiguration | Impact | Prevention Strategy |
|---|---|---|
| Open Storage Buckets | Data Exposure | Regular Audits |
| Weak IAM Policies | Unauthorized Access | Strict Role Definitions |
| Exposed APIs | Data Breaches | API Gateway Controls |
Lastly, future-proofing your cloud security is an ongoing journey rather than a destination. By continually revisiting your security posture, adapting to new threats, and investing in the right tools and training, you can transform your cloud environment into a resilient fortress against the myriad challenges that lie ahead. Embrace change and empower your organization to thrive in an ever-evolving digital landscape.
Taking the First Step: Implementing a Cloud Posture Management Plan Today
In today’s fast-paced digital landscape, the significance of a robust cloud posture management plan cannot be overstated. Organizations are increasingly migrating their operations to the cloud, making the need for a proactive approach to security more critical than ever. Misconfigurations can not only expose sensitive data but also lead to devastating breaches that can tarnish a brand’s reputation. Taking the first step towards implementing an effective cloud posture management strategy is essential in safeguarding your assets.
To start, assess your current cloud environment. This involves a thorough evaluation of your cloud infrastructure, configurations, and policies to identify vulnerabilities. Consider the following key areas:
- Access Controls – Review your identity and access management setups to ensure that only authorized personnel have access to sensitive data.
- Configuration Management – Regularly audit your cloud configurations against industry best practices to detect any deviations.
- Compliance Regulations – Stay updated with compliance standards relevant to your industry, ensuring your cloud practices align with legal requirements.
Once you have a comprehensive understanding of your cloud landscape, the next step is to establish a continuous monitoring system. This system should include automated tools that can detect misconfigurations in real-time, offering immediate alerts for potential threats. By integrating tools such as Cloud Security Posture Management (CSPM), you can enhance your visibility into cloud environments, allowing for:
- Proactive Risk Management – Anticipate and mitigate risks before they result in breaches.
- Enhanced Visibility – Gain insights into the security posture across all cloud resources.
- Compliance Automation – Streamline compliance checks and audits, reducing manual overhead.
Moreover, training your team on cloud security best practices is paramount. Empowering employees with knowledge and awareness can reduce human errors that often lead to misconfigurations. Create regular training sessions that focus on:
- Cloud Security Fundamentals – Educate staff on the basics of cloud security and its importance.
- Incident Response Protocols – Ensure everyone knows how to respond effectively in the event of a security incident.
- Configuration Best Practices – Share guidelines for maintaining secure configurations in cloud services.
cultivate a culture of security within your organization. Make it a priority at every level, from executive leadership to individual contributors. A unified approach will not only enhance your cloud security posture but also foster an environment where everyone feels responsible for protecting sensitive data. By making security a shared value, you create a formidable defense against misconfigurations and potential data breaches.
Frequently Asked Questions (FAQ)
Q&A: Misconfigurations Are the New Data Breach: How Cloud Posture Management Helps
Q: What do you mean by “misconfigurations are the new data breach”?
A: In today’s cloud-centric world, misconfigurations—errors in the setup of cloud environments—have become a leading cause of data breaches. Unlike traditional breaches that often involve sophisticated hacking techniques, these misconfigurations arise from human error, oversight, or lack of knowledge. They can expose sensitive data to the public or leave systems vulnerable to attacks. This shift underscores the need for organizations to recognize the risk of misconfigurations as a significant threat to their data security.
Q: How prevalent are these misconfigurations?
A: Alarmingly prevalent! Various studies indicate that as much as 70% of cloud security incidents are attributed to misconfigurations. This statistic highlights a critical challenge for organizations managing cloud environments. With the rapid adoption of cloud services, businesses often overlook the configuration settings, leading to vulnerabilities that attackers can exploit. It’s a wake-up call for organizations to take a proactive approach to their cloud security.
Q: What is Cloud Posture Management (CPM), and how does it help?
A: Cloud Posture Management (CPM) is a comprehensive approach to ensuring that your cloud environments are configured securely and remain compliant with best practices and regulations. CPM continuously monitors cloud configurations, identifies vulnerabilities, and provides actionable insights to correct any misconfigurations before they can be exploited. By adopting CPM, organizations can shift from a reactive to a proactive security posture, significantly reducing the risk of data breaches.
Q: Can you share some examples of how CPM has helped organizations?
A: Absolutely! One notable case involved a large retail organization that suffered from frequent misconfigurations leading to unauthorized data access. By implementing CPM, they could automatically detect and rectify vulnerabilities in real time. As a result, they not only improved their security posture but also built a culture of accountability and vigilance within their IT teams. This transformation not only protected their customer data but also enhanced their brand reputation and customer trust.
Q: Why should organizations invest in Cloud Posture Management now?
A: The threat landscape is evolving rapidly, and the costs associated with breaches—financially and reputationally—are staggering. Organizations that invest in CPM now position themselves ahead of the curve, safeguarding their assets and empowering their teams with the tools they need to ensure security. Moreover, as regulatory requirements grow stricter, having a robust CPM strategy will not only protect data but also ensure compliance, avoiding hefty penalties and fostering customer loyalty.
Q: What steps can organizations take to start implementing Cloud Posture Management?
A: Organizations should start by assessing their current cloud security posture. Engaging with a trusted CPM provider can help identify specific vulnerabilities and tailor a strategy that aligns with their unique environment and business needs. Additionally, fostering a culture of continuous learning and training around cloud security best practices is essential. By empowering your teams and leveraging advanced technologies, organizations can turn their cloud infrastructure into a fortress rather than a target.
Q: In one final thought, what is the ultimate takeaway regarding misconfigurations and Cloud Posture Management?
A: The ultimate takeaway is that in a world where data is invaluable, misconfigurations can no longer be seen as mere oversights—they are critical vulnerabilities that can lead to devastating consequences. Cloud Posture Management is not just a tool; it’s a mindset that embraces security as a continuous journey. By investing in CPM, organizations can transform their approach to cloud security, turning potential risks into opportunities for growth and innovation. Together, we can build a safer digital landscape for all.
The Conclusion
As we navigate an increasingly complex digital landscape, the importance of robust cloud security cannot be overstated. Misconfigurations have emerged as a significant threat, often serving as the gateway for devastating data breaches that can compromise not just sensitive information, but also the trust and integrity of organizations. However, there is hope. By embracing Cloud Posture Management, businesses can turn the tide against these vulnerabilities, proactively identifying and correcting misconfigurations before they lead to catastrophic consequences.
The path forward involves a commitment to continuous improvement and vigilance. By prioritizing a strong security posture, organizations not only safeguard their data but also empower their teams to innovate without fear. Remember, the journey toward optimal cloud security is not just about technology; it’s about fostering a culture of accountability and awareness. Let us champion the cause of proactive security measures and ensure that misconfigurations are no longer the silent saboteurs of our digital age.
the message is clear: take action now to secure your cloud environment. Invest in Cloud Posture Management and join the ranks of forward-thinking organizations that prioritize security and resilience. Together, we can transform the challenge of misconfigurations into an opportunity for growth and security, paving the way for a safer, more secure digital future. The time to act is now—let’s rise to the challenge and protect what matters most.